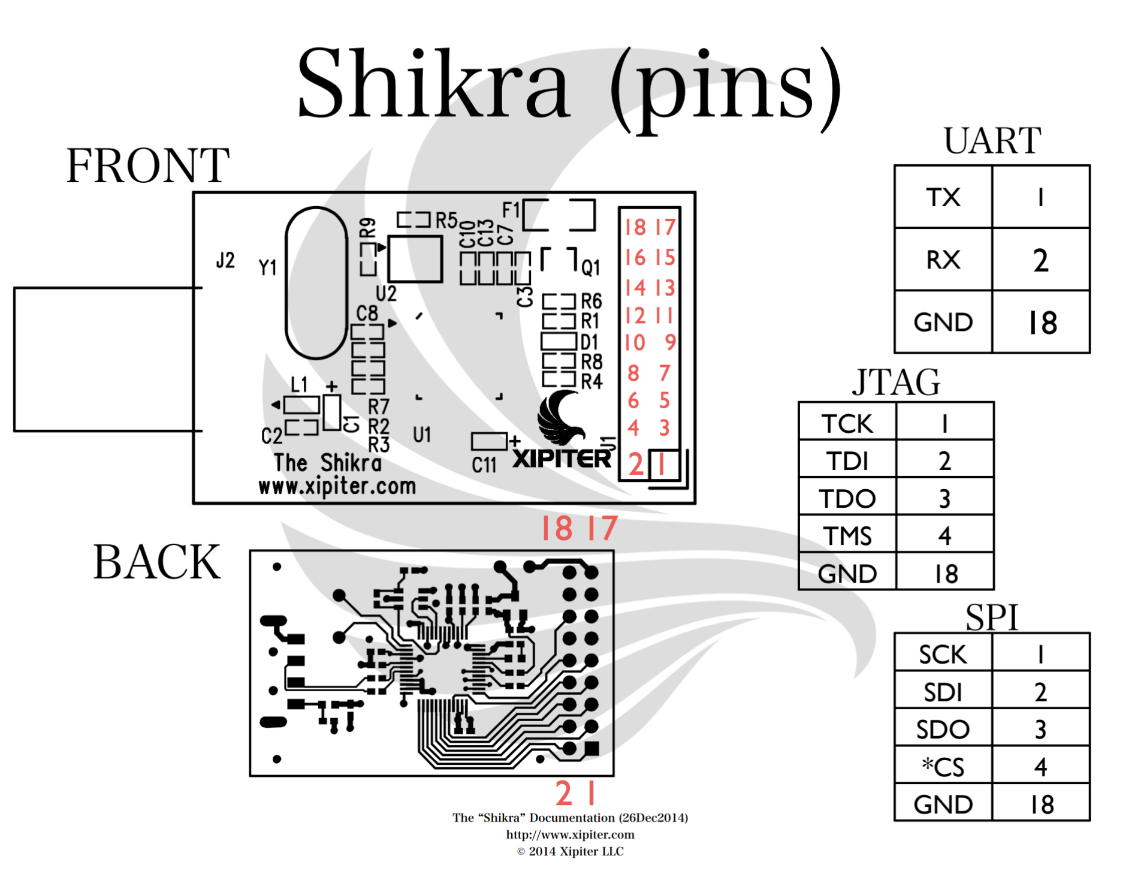
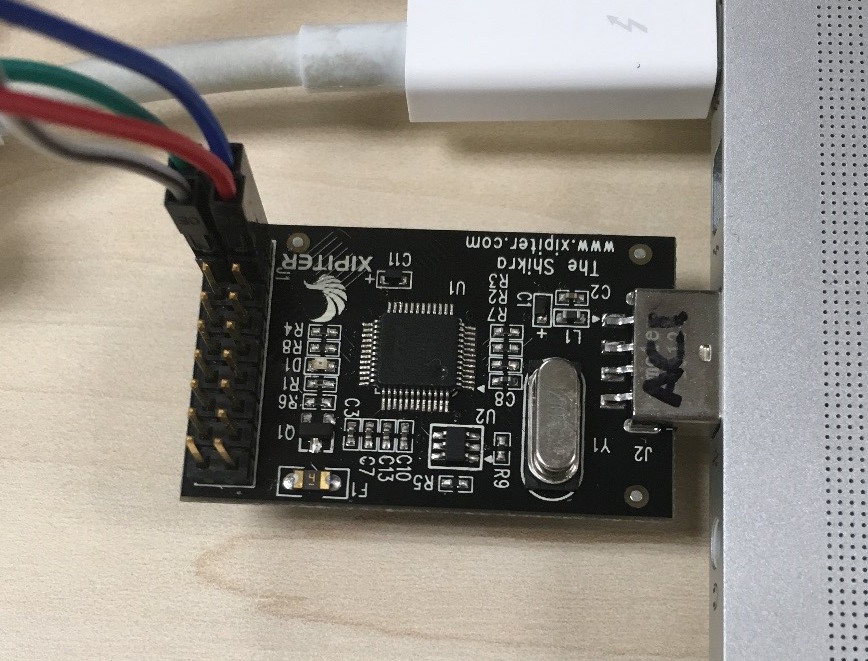
Senrio on Twitter: "The Shikra (https://t.co/zB30To5h0u) has arrived for : http://t.co/ZUbqUXrG48 No embedded devices are safe. http://t.co/bZWyImRXEu" / Twitter

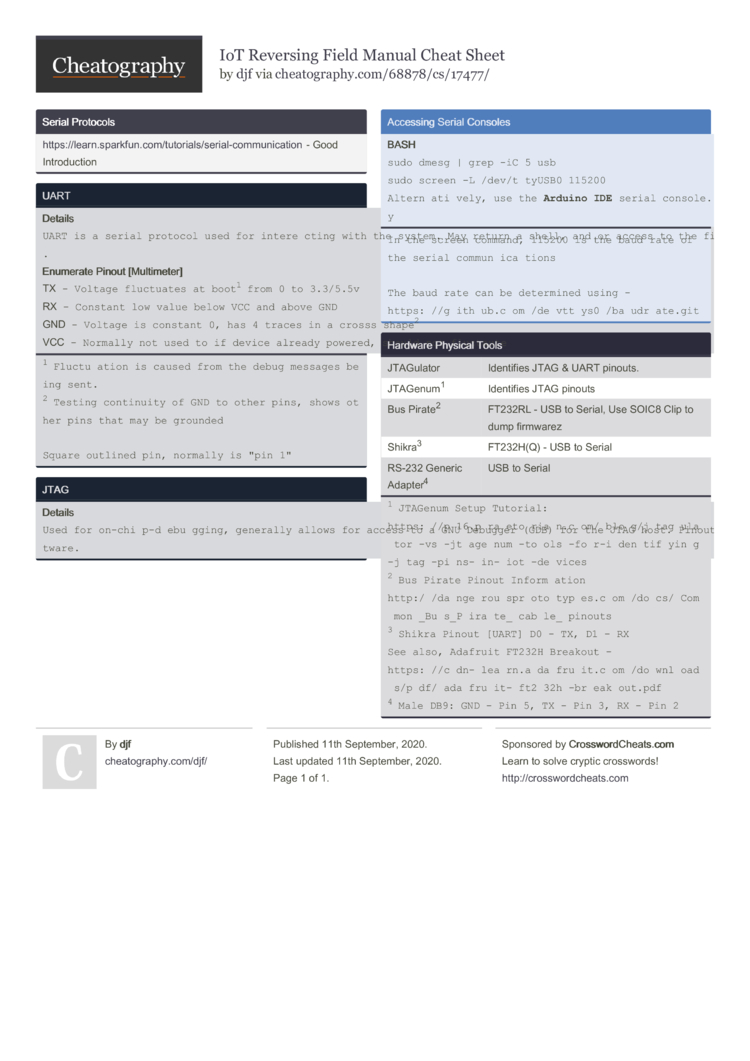
Assessing the security of a portable router: a look inside its hardware, part deux | Malwarebytes Labs

hackerfantastic.crypto no Twitter: "Used @XipiterSec Shikra FT232H breakout after JTAG locating pins, EJTAG MIPS seen in OpenOCD 😍 https://t.co/DixJ4DxA5u" / Twitter
GitHub - Xipiter/shikra-programmer: Shikra (http://int3.cc/products/the- shikra) programming utility